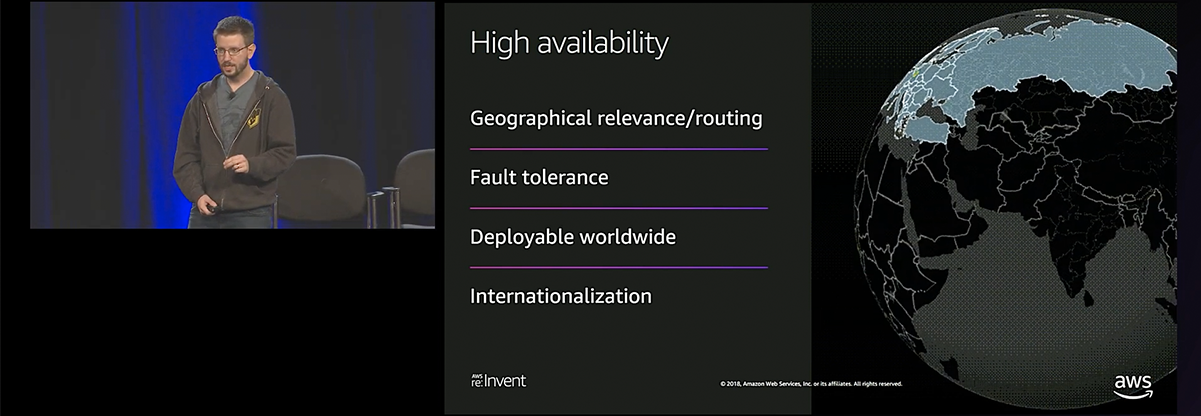
Hey there! I’m Tyler "Riot Adabard" Turk, Senior Infrastructure Engineer, and I work on the Player Accounts team at Riot. The Player Accounts team is responsible for every player's ability to log in and manage account data, and we recently re-architected our system to become GDPR compliant, provide a better player experience, and enable Riot to become a multi-product company in the future.
Hi, I’m Tony Albrecht, an engineer on League. I’m back with some more performance goodness. In the previous article, we tracked a slowdown reported in an LCS game and an issue with Swain that was first reported by players. For this article, we’re stepping back a little further and looking at how we can measure the aggregate performance of League over an entire region, notice a dip, and then narrow down the cause. In this case, we chased a 2ms per frame drop in performance to a single missing ASCII character in our code.

Hey there. I’m Stephen “Riot FloofyRice” Zhang and I’m a technical developer in QA on the Content Efficiency team, which focuses on building internal tools. I want to talk about our efforts to clean up one of our bigger problems at Riot: data debt.
Hi, I’m Tony Albrecht, an engineer on League. You might remember me from such articles as Profiling: Measurement and Analysis and Profiling: Optimisation where we looked at how we find and optimise performance bottlenecks in the LoL code base. In this article, we’re going to take a step back and look at how we detect and then fix real world performance issues that slip out past our QA and monitoring systems and escape into the wild to plague you, The Player.

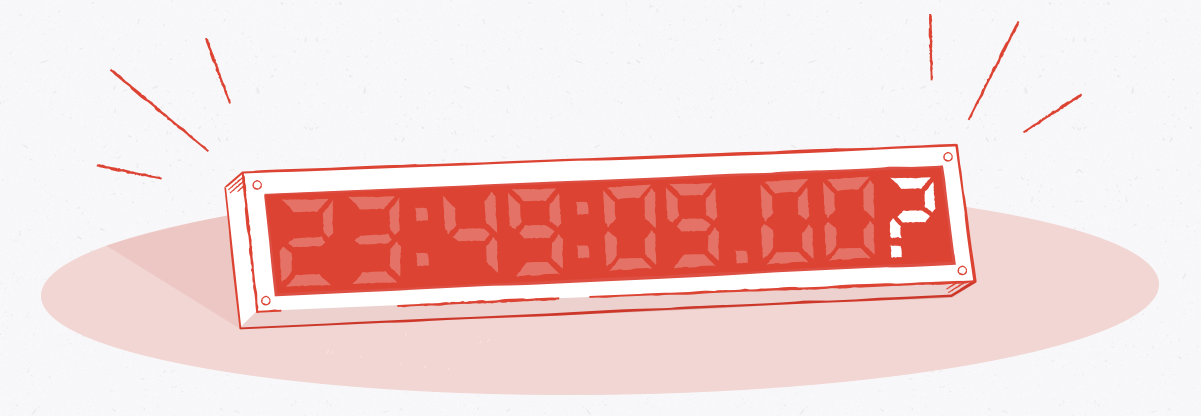
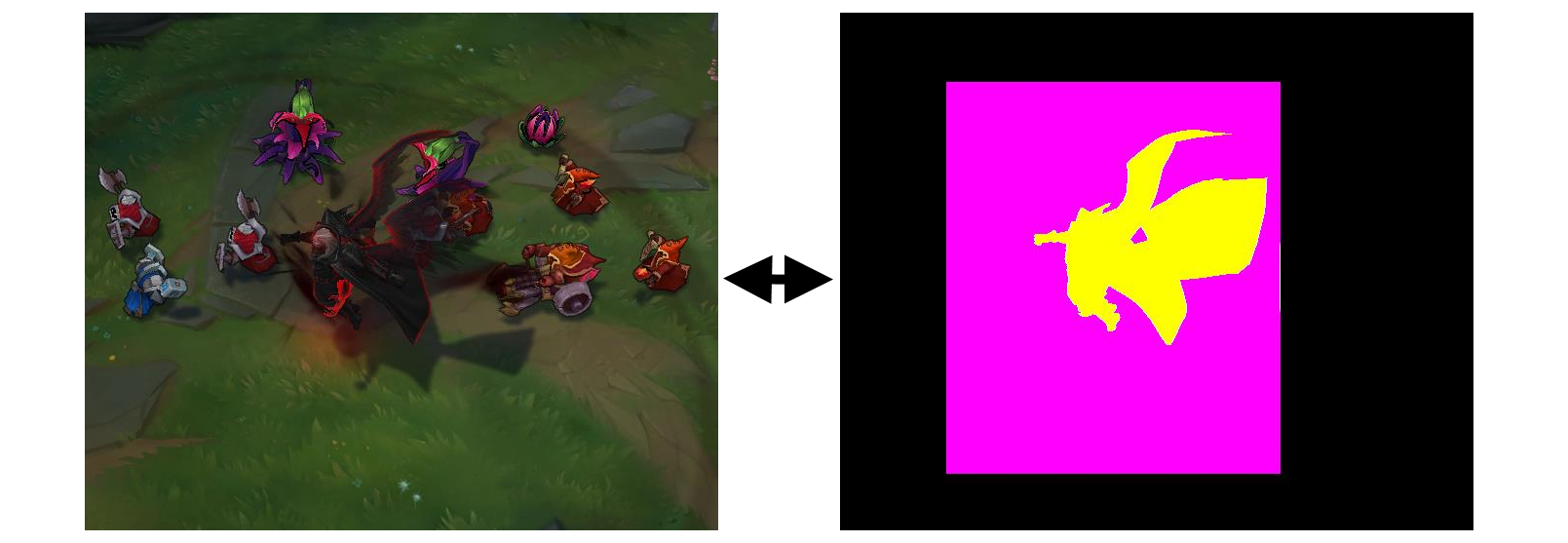
Combating cheats is an ever-evolving arms race. The scope and complexity of cheat development grows every year along with the stakes in online gaming. The pressure is on for game studios to level up when it comes to detecting and preventing bad actors. I’m Michael “Perma” VanKuipers, and I used to be one of those bad actors; I spent over a decade developing cheats for various games and earned the ire of at least one large game studio in the process. These days I work on Riot’s Anti-Cheat team, helping secure League of Legends from scripts, bots, and exploits.
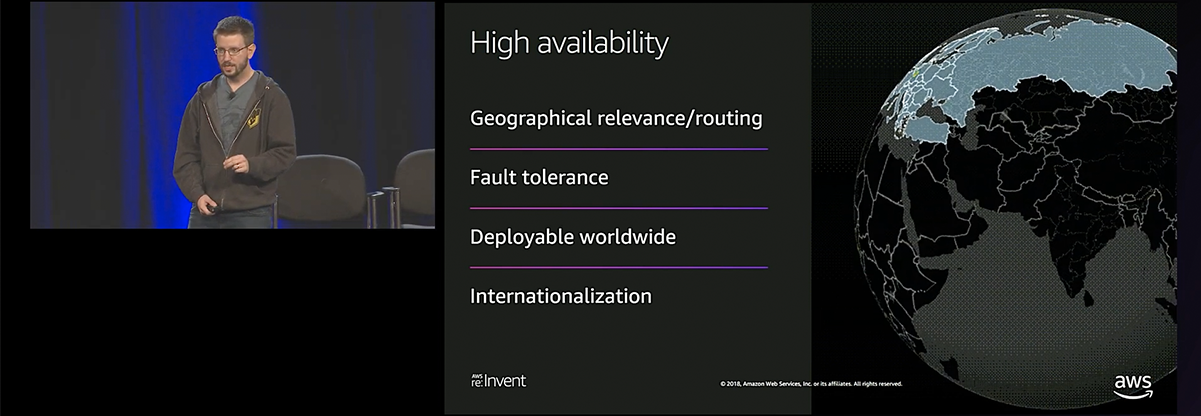
It’s been over two years since I first wrote an article discussing how we combined Docker containers and Jenkins to create ephemeral build environments for a lot of our backend software at Riot Games. Today the series is seven articles strong and you’ve rewarded us with feedback, conversation, technical insights, tips, and stories about how you too use containers to do all kinds of interesting things. In the world of technology, two years is a long time. The series, while still useful, is out of date. Many of the latest Docker doodads and gizmos are absent.

The price of determinism is eternal vigilance.
I’m Rick Hoskinson, an engineer on the League of Legends Core Gameplay Initiative, and this is the final article in the “Determinism” series. Previously in this series, we explained the broad strokes required to achieve determinism in the League of Legends game server. However, there remained the task of tracking down the remaining divergences in legacy code while building maintainable systems that would ensure future divergence regressions could be found and fixed. Thoughtful implementation of these systems allows us to sustain Project Chronobreak features without dedicating a full-time team.
In this final article, we’ll dig into how we detect divergences and fix them.

Hi there. I’m Bill “LtRandolph” Clark, and I’m the engineering manager for the Champions team on LoL. I’ve worked on several different teams on League over the past years, but one focus has been consistent: I’m obsessed with tech debt. I want to find it, I want to understand it, and where possible, I want to fix it.

Hi, I’m Tony Albrecht, an engineer at Riot, and I’m a performance junkie. This is the second part in a series on how to optimise your code. In Part 1, Measurement and Analysis, we learned how to find and analyse performance bottlenecks in our sample code. We surmised that the issue was due to slow memory access. In this article we’ll look at how we can reduce the cost of memory accesses and thereby speed up our program.
The League of Legends client UI resembles many traditional web applications, both in its choice of technology (JavaScript/HTML) and its range of functionality. However, the League client (the pre-game experience) is not a traditional web app - at its core it’s a game UI with high-quality visuals, which led to several interesting challenges along the way. I’m Richard Ye, a software engineer on the League of Legends client, and I’m going to talk about one of the major development challenges we encountered in the client UI: animation.